Join our Proxy Reseller program
Want to enter the residential proxy business, but don’t really know where to start? Partner with us and resell our residential proxies with our powerful and simple-to-use API.
Read More
Our sizeable pool of residential proxies gives you the highest authority and an unmatched commitment to ethics for larger projects.

Our ISP proxies give you the authority of residential proxies and the speed of data center proxies for non-scraping use cases.
Our award-winning data center proxies give you 99% uptime and swift speed for many use cases out there.

Our mobile proxies give you continuous internet connectivity and a seamless browsing experience for various scraping projects.
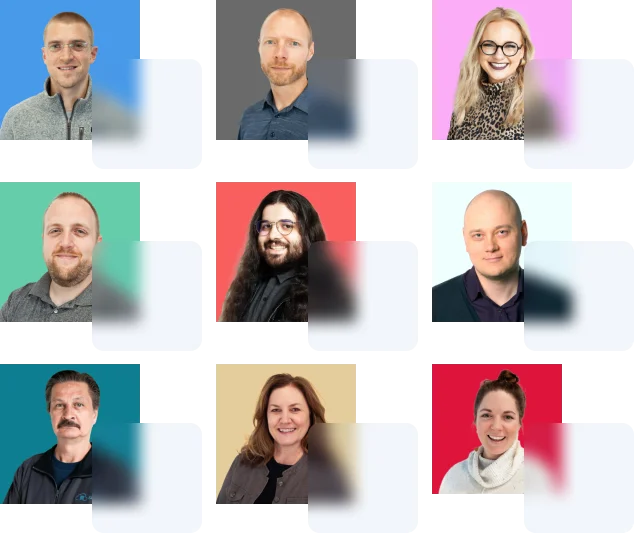
At Rayobyte, we don’t just want to be your proxy provider – we want to be your proxy partner, dedicated to going above and beyond to ensure you have a great experience.

“The proxies perform well and Rayobyte sticks to its strict ethical code.”
Read moreWant to enter the residential proxy business, but don’t really know where to start? Partner with us and resell our residential proxies with our powerful and simple-to-use API.
Read MoreWe help small companies scrape millions of websites, government agencies aggregate data from across the web for analitics, and Fortune 500 companies scrape literally billions of products on eCommerce sites. No matter the size or use case, Rayobyte proxies can help you!
Read MoreRayobyte is a pioneer in ethical web data collection. Our commitment to ethics is also recognized by the only international body in the industry.
Read moreWe are real people who work tirelessly to make you and your business a success. Talk to real dedicated account managers who will help you find the best proxies for your use case. You’ll never need to worry about where your proxies are coming from!
Read More